My advice to you would be to stick with the editor’s pick. Well, now it’s time to fire up Tails and do a little bit of tinkering. When you’re ready, hit the Close button and you’re all set. Review the info and hit Create when you’re done. For this tutorial, I’ve used Universal.
How Do I Verify An Onion Link Is Safe?
Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic. After installation, you can use Tor to access the public internet as well as .onion websites. After your data is secured inside multiple layers of encryption, your web traffic is transmitted through a series of network nodes, called onion routers. Powerful antivirus software with advanced Dark Web Monitoring Features like Norton 360 Deluxe can help keep your internet browsing private and secure.
The term “Dark Web” often arises in discussions surrounding online anonymity, and it is crucial to understand its place within the broader internet landscape. This masking is achieved through a sophisticated process known as onion routing, where web traffic is encrypted in multiple layers and channeled through a global, volunteer-operated network of relays. This network, often referred to as the “Onion Router,” provides a unique pathway for internet traffic, effectively masking the user’s identity and geographical location. In 2002, the dark web grew significantly when researchers supported by the US Naval Research Laboratory built and released the Tor network. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. And with many unfamiliar-looking sites on the dark web, it’s harder to distinguish safe websites from shady ones, and easier to fall victim.
Accessing the dark web itself is not illegal, as it is merely a part of the internet not indexed by standard search engines. This extra layer of security can deter potential hackers from gaining unauthorized access to sensitive data. Understanding how dark web websites function is essential for safely browsing the dark web. These search engines operate similarly to regular search engines but index content from within the dark web’s encrypted network.
More In Internet And Social
If you know what you’re doing, you can configure Firefox to route its traffic through the Tor network. Plus, all your internet traffic is automatically routed through the Tor network, so you're protected from the moment you start using it. Unlike Tor, which lets you access both the regular web and .onion sites, I2P is more focused on its own internal ecosystem.
The Tor Browser works by routing internet traffic through a global network of server nodes to mask your IP address and activity. While Tor offers strong privacy protections, it comes with notable drawbacks that can make it impractical for everyday use, and the dark web content it grants access to can put users at risk. That’s why savvy Tor users go a step further, encrypting all their internet data via a VPN first — a set-up known as “Tor over VPN” — adding a powerful extra layer of privacy that masks both your IP and Tor usage. Tor, short for “The Onion Routing project,” is a free, open-source network built to protect online privacy and enable access to the dark web.
Because these sites are unregulated by major internet services and domain providers, they can host a number of potential hazards, including malware and illegal material. It develops open-source software that encrypts and routes internet traffic through a global volunteer network to protect users against surveillance and censorship. Many major companies have reserved .onion domains and host websites there, and there is a list of onion services on Wikipedia.
This means Tor is a lousy option for streaming video, online gaming, or downloading files (torrenting). While this doesn’t tell the exit node what your original IP address or your geographical location is, it could spy on your activity if the website you’re visiting isn’t a secured HTTPS website. While this isn’t an issue for most of the trip (since each relay only has access to the previous and next relays in the network), it is an issue with the exit node. Since each node server in the Tor network is volunteer-operated, you never know who operates the relays that your data is traveling through. While the Tor Browser and the Onion Network are an excellent way to protect your online privacy and anonymity, it is by no means a perfect solution, and it has a few weaknesses. In an onion network, messages are encased in layers of encryption, much like the layers of an onion.
Download Tor Browser
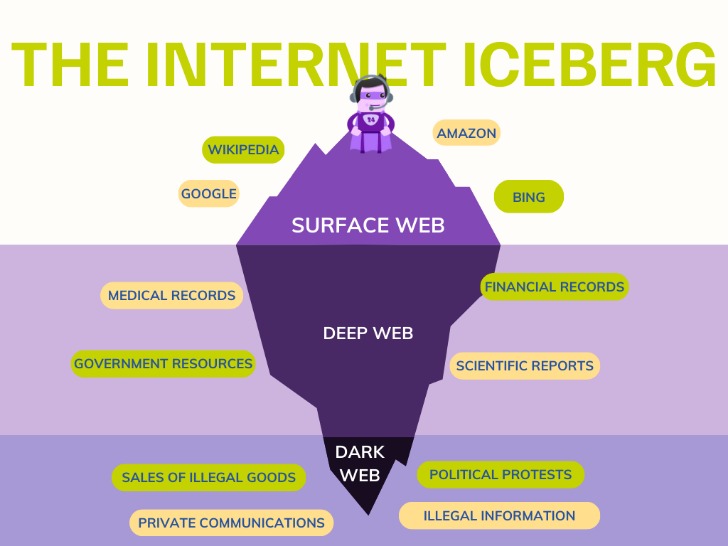
For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. More than that, though, the dark web contains content and data that can be accessed anonymously. Websites and data on the dark web do typically require a special tool to access. As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. This can include medical records, research papers, private forums, and networks.
- If you feel a browser just won’t cut it and want to keep your dark web browsing activity as private as possible, Whonix might be for you.
- The Tor network combined with a VPN is one of the safest ways to get on the dark web.
- If you want to improve your security further, you could also use a VPN at the same time as Tor.
- With TecnetOne, you see what others don’t—and act before it’s too late.
- There’s evidence that law enforcement agencies in freer countries operate many exit nodes for monitoring and surveillance purposes.
First, Install A Reliable VPN
Web crawlers run the regular internet, scouring the web to discover newly published websites or pages in a process called crawling. The dark web is a small subset of the deep web comprising purely non-indexed websites and services. It comprises websites that aren’t easily accessible mainly because they are non-indexed, password-protected or paywalled.

Is Tor Really Safe?
Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Dark web websites also use a scrambled naming structure that creates URLs that are often impossible to remember. Dark web websites look pretty much like any other site, but there are important differences. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”.
What Is Tor Browser?

Research what they offer and assess your privacy needs to make a decision about which dark web browser works best for you. While both tools enhance online privacy, they work differently. When using Tor, practice good security hygiene by avoiding suspicious links and using reliable antivirus software. Using Tor and the Tor Browser is considered relatively safe if you use the default security settings, but keep in mind that Tor does not provide end-to-end encryption. Tor is completely legal in many places, including the U.S., EU, UK, and Australia, but illegal in others, like China and Russia. Get Norton VPN today to start browsing the web more freely and anonymously.
A Step-by-Step Guide To Access The Dark Web – Trusted Insights From TorConnect
- Tor Browser sends web traffic through an entry node (blue), middle node (green), and exit node (orange) to encrypt and decrypt traffic.
- On the Dark Web, you will not find search results indexed by Google, which can make it difficult to find what you are searching for.
- Or hidden internet directories such as the Hidden Wiki are good sources to look at as they feature different types of dark web links.
- Outside or inside Tor, your traffic is secured 100% of the time.
Finally, users whose internet connection relies on a proxy server can configure these settings within the “Configure Connection” window as well. The “Safer” level disables certain website features that are often exploited for malicious purposes, such as JavaScript on non-HTTPS sites, and requires click-to-play for audio and video content. Beyond connection settings, Tor Browser offers basic configuration options for enhancing privacy and security during browsing.
We're a nonprofit organization and rely on supporters like you to help us keep Tor robust and secure for millions of people worldwide. Tor Browser already comes with HTTPS-Only mode, NoScript, and other patches to protect your privacy and security. Therefore, while Tor provides a strong layer of privacy, it is not an absolute shield against surveillance, and users should remain aware of this possibility. Fraudulent services, such as fake hacking services, counterfeit document vendors, or Ponzi schemes promising unrealistic returns, are also prevalent. Due to its largely unregulated nature, the probability of encountering scams is significantly greater than on the regular internet. The risk of infection is considerably higher compared to the surface web due to the lack of regulation and security oversight.
For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing. I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication.
It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. These pages come with extra protections for user anonymity and data security, and you need special software to access them—you can't get at them through your normal web browser, like you can with much of the rest of the deep web. In addition to the categories below, I exclusively cover ad blockers, authenticator apps, hardware security keys, and private messaging apps. You can still be tracked at network entry and exit nodes, as indicated by reports that police identified Tor users by surveilling data centers.
This browser, on paper, provides anonymity by routing your traffic through different secure nodes, preventing tracking and surveillance. Tor is a Firefox-based browser made specifically to enable access to onion sites, hence the name The Onion Router. The Tor browser is your gateway to the dark web, allowing you to access .onion sites anonymously. While the Dark Web might be home to a wealth of valuable information and services, it’s also notorious for being incredibly dangerous.



