Through the dark web, users in places of high censorship can also access information and news. The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on.
Related Articles From The Safe Browsing Section
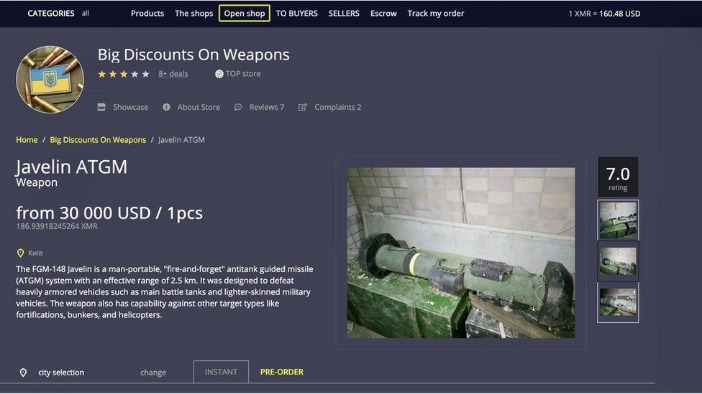
You can see all the product categories the marketplace deals with on the homepage. Empire Market is a dark web shop that resembles the AlphaBay marketplace. However, you must wait some time to reassess this marketplace because it’s been shut down. The website allows visitors to view all the goods and services on display before they buy something. DarkOde Reborn is a great darknet market where you can find anything you want.
Is It Illegal To Visit And Use Dark Websites?
These systems provide a clear, crowd-sourced metric of reliability and product quality, significantly de-risking transactions for buyers. Modern digital storefronts feature streamlined interfaces that categorize products with a precision rivaling mainstream e-commerce, allowing for efficient browsing and selection. This practice eliminates the need to rely on third-party directories, which can often be outdated or compromised. These technical redundancies function as backup access routes, automatically compensating for any single point of failure that may be taken offline by routine maintenance or external pressure. This multi-link approach effectively counters takedown attempts and network filtering, providing a resilient framework for commerce.
Modern platforms have moved beyond basic anonymity to integrate sophisticated cryptographic protocols directly into their architecture, ensuring that user data and transaction details remain confidential by default. These sites maintain a consistent presence, and the darkmarket list for 2025 indicates a robust network of active dark websites. This primary categorization allows users to quickly narrow their search to a specific class of product. A market's ability to provide and maintain these access points is a direct reflection of its infrastructural stability and commitment to secure digital commerce.
- This technical infrastructure ensures that participation in these economic platforms remains a private matter between the buyer and the vendor, fostering a free market based on mutual agreement.
- Leading markets now maintain a network of rotating mirror links and provide users with official onion service directories, ensuring consistent access even if a primary URL is compromised.
- Microsoft Word is one of our favorite word processors because it's versatile and lets you craft simple documents or wonderful stories with ease.
- What makes these marketplaces particularly tricky is the level of anonymity they provide; both buyers and sellers use encryption methods to protect their identities and transactions.
- AI-as-a-service (AIaaS) platforms offer many of these capabilities that lower the barriers for cybercriminals to carry out these attacks.
How Brandefense Helps Mitigate These Threats
This enhanced reliability directly contributes to the market's growth, allowing for sustained commercial activity and the development of long-term vendor reputations. This end-to-end streamlining transforms the acquisition process into a predictable and reliable activity, focusing on the transactional efficiency and quality assurance that define modern darknet commerce. The system is built around the use of Bitcoin and other cryptocurrencies, with integrated wallets and automated escrow services.
Bitcoin's Role In Secure Darnket Trade
The May 2019 seizure of news and links site DeepDotWeb for conspiring with the markets created a temporary disruption around market navigation. From then on, through to 2016 there was a period of extended stability for the markets, until in April when the large Nucleus marketplace collapsed for unknown reasons, taking escrowed coins with it. In March 2015, the Evolution marketplace performed an "exit scam", stealing escrowed bitcoins worth $12 million, half of the ecosystem's listing market share at that time. In October 2013, Project Black Flag closed and stole their users' bitcoins in the panic shortly after Silk Road's shut down. The shutdown was described by news site DeepDotWeb as "the best advertising the dark net markets could have hoped for" following the proliferation of competing sites this caused, and The Guardian predicted others would take over the market that Silk Road previously dominated. Silk Road's use of all of Tor, Bitcoin escrow and feedback systems would set the standard for new darknet markets for the coming years.
Illicit Marketplaces
To ensure resilience, reputable markets provide multiple verified mirror links, which are alternate addresses that lead to the same platform. The resilient infrastructure of Nexus Market is a primary factor in its high ranking among darknet platforms. Users should always verify these links through multiple independent sources, such as darknet forums or link aggregators, to avoid phishing attempts. The fundamental appeal of cryptocurrency transactions within the darknet ecosystem lies in their inherent cryptographic security. The platform's official url and multiple mirror links ensure consistent access to its digital store, facilitating a reliable ecosystem for commerce.
Reliable Access For Safe Darknet Shopping
Of course, all transactions are anonymous and Bitcoin-driven. Hidden Wiki’s not the only search engine online. You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”. If you’re feeling chatty, you can always access a chat room. My advice to you would be to stick with the editor’s pick.
Acronis Cyber Protect Cloud: New Version C2505
It blends illegal trade with features like gambling, all while maintaining a clear and accessible structure. Vortex aims to stand out by being user-friendly, secure, and anonymous. During our tests for the research, we were able to register with a bogus email and a random username. It offers a wide range of goods and services with robust anti-DDoS protection (with military-grade security protocols) and no JavaScript, ensuring privacy and uptime. The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. (Having Tor is a must because without it, you cannot access any onion website.)
The primary onion address serves as the main entry point, but its availability can be intermittent. Platforms mitigate the risks of service disruption from technical issues or external pressure by establishing a system of official URLs and mirror links. The checkout process is equally simplified, often mirroring the familiar steps of clearnet e-commerce sites, which reduces cognitive load. Platforms like Nexus Market prioritize a design philosophy that minimizes user error and maximizes clarity. The market integrates end-to-end encryption for all communications and mandates multisignature escrow for financial dealings.
Darknet Markets – Dark Web Links
Formerly known as Archive.is, it is one of the best onion sites on the dark web. The downside is that it limits data to only 25mbps per user. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. RiseUp is a top dark web website that offers secure email services and a chat option. Using the ProtonMail .onion site offers security and privacy advantages. Furthermore, data will help to detect attacks against the network and possible censorship events.
Dark Web Marketplaces Vs Open Web Criminal Forums
Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. It can only be used to access the content uploaded to the Hyphanet, which is a peer-to-peer distributed data store. Like I2P, Hyphanet is a self-contained network within the network that can’t be used to access sites on the public web. It can only be used to access hidden services specific to the I2P network.



