That means you can access .onion sites without even opening the Tor browser. We tested them with Tor, hit multiple .onion sites, and didn’t flinch. Whether you’re digging into whistleblower leaks, downloading files via secure .onion links, or just curious about what lives beyond the Google index, you need to lock in a VPN first. Do you want to access the Onion sites with multiple devices?
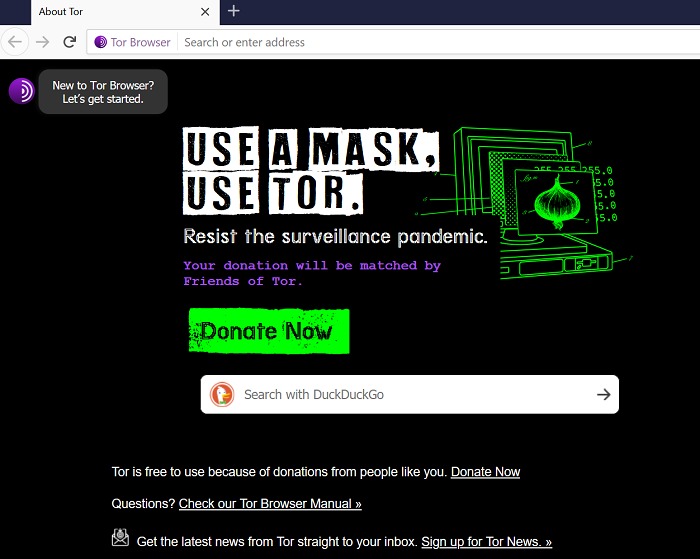
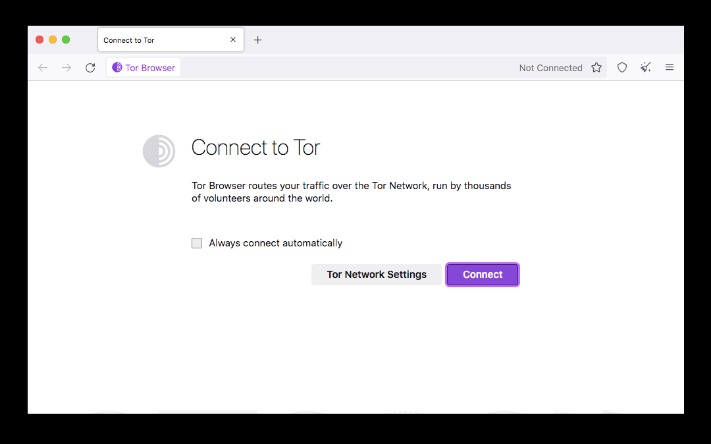
You can also use Tor to enjoy better privacy online, but I honestly think a VPN is better suited for that. The Tor browser is mostly used to surf the dark web or evade censorship. Repeat this process until you get an IP address from your desired country. Access any site you want as you normally would on your regular browsers. You can now start surfing the web while connected to the Tor network.
Check onion links through trusted directories, user reviews, and reputation checks. Tor encrypts your traffic and routes it through multiple volunteer-operated relays, making it difficult to trace. Use directories like The Hidden Wiki or Dark.fail, which list verified and regularly updated onion links. Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor.
Top 10 Best Dark Web Search Engines In 2025 Safe & Anonymous Browsing Tools For Tor Users
These are the final stops in the Tor relay chain before your traffic hits the open web. And in countries where Tor use is flagged or monitored, that’s already a red flag. They don’t know what you’re doing, but they know you’re doing something. On that note, if you’re having trouble telling the two apart (including their strengths and weaknesses), check out our comparison of Tor and VPNs. While Tor does a solid job anonymizing your traffic, there are still gaps, and that’s exactly where a VPN steps in. Not just to stay anonymous online, but to stop your ISP, government, or even opportunistic creepers from tracking your every move.
Internet users can surf the dark web anonymously thanks to specialized darknet browsers. In this guide, we delve into the top 10 darknet browsers of 2023, evaluating their privacy, security, and user-friendliness. Versatile copywriter Heidi Edwards, a marketing graduate from WGU, crafts compelling content across diverse sectors, from eco-conservation to tech.
- This is then built upon using highly advanced cryptographic tools to add the protective layers that ensure you stay hidden while browsing the internet.
- We believe everyone should be able to explore the internet with privacy.We are the Tor Project, a 501(c)(3) US nonprofit.We advance human rights and defend your privacy online through free software and open networks.
- In fact, I2P designed its own domain ending structure, called “eepsites.”
- The dark web is definitely not a safe place to be around, especially for the ones who are not very much aware of the hidden zone of the internet.
Before diving into how these browsers function or which ones are worth your trust in 2025, it’s important first to understand what dark web browsers actually are. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship. Your traffic is relayed and encrypted three times as it passes over the Tor network. All anyone monitoring your browsing habits can see is that you're using Tor. Tor Browser prevents someone watching your connection from knowing what websites you visit.
Should You Try Tor Browser?
Encrypt your connection and protect your data with AVG Secure VPN Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Military-grade encryption guards you on public Wi-Fi, and location selection helps you stream the content you want.
Setting Up I2P (Invisible Internet Project)
It conceals your location and other personal data that are exposed when using standard browsers. The Tor browser routes your online requests through multiple nodes to obscure them from prying eyes. Several accessible plug-ins can give a terrific experience to the users. The sites are identified by the Public Key than by IP address. The data is encrypted using a distributed network making the user totally untraceable to performing deep web login and surfing.
Unlike other search engines, it does not collect or share web activities and personal data of users. Thankfully, some useful sites can help you circumnavigate the dark web landscape as you search for the best content. It has onion links you cannot access with regular browsers like Chrome, Firefox, Edge, or Safari. This article lists some of the best dark web websites you can visit securely. Though people usually think of dark websites as the wrong online place, that’s not the complete truth. This so-called “Tor over VPN” set-up adds an extra layer of security, which can be especially important on monitored or public networks.
How To Install The Tor On Android
Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine.
For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing. Dark web sites via Tor have unique URL structures that end in .onion. Accessing the Tor network through Tails OS (The Amnesic Incognito Live System) on a thumb drive is a highly secure way to browse the dark web anonymously. In this method, your traffic is routed through Tor before it reaches the VPN server, masking your IP address even from the VPN provider.
The dark web facilitates activities such as the sale of illegal goods, hacking services, and forums for anonymous communication. It is a subset of the deep web and is known for its anonymity and privacy features. However, for this to work, you’re going to need the right browser for the job.
NordVPN – Best VPN For The Dark Web Overall (via Free Trial)
They take proper care of your privacy, your search histories, and further data. It deletes all your data after every successful web surf, starting from search history to passwords. Regarding security, Tor Browser establishes a completely secured network with several layers of fake IPs. Freenet is an anonymity-based network for the dark web links utilizing free software to fight censorship of information and protect freedom of speech.
Still, Tor and the dark web have a stigma attached due to the undercurrent of illegal activities. Although Tor is a sophisticated privacy tool, it has several disadvantages — some of which counteract its cybersecurity advantages. Use Tor alongside a VPN to ensure your web traffic is fully encrypted. And at the exit node, your decrypted traffic is vulnerable to interception. Anyone who owns and operates the entry node will see your real IP address. Plus, Tor cannot protect against tracking at the entry and exit nodes of its network.
Downloading And Installing Tor On Your Operating System: A Step-by-step Guide
Hence, you never know when a popular .onion site is going to vanish, or even die. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies. The US Navy’s main reason for creating Tor was to help informants relay information safely over the internet.
How To Stay Safe While Using Tor Browser
Sometimes, you can access a website but won’t be able to login on your Tor browser. If you must use one, ensure it’s a VPN with a strict, independently audited no-logs policy. A VPN app opens another potential vulnerability, as it can log the sites you visit via Tor. A common inquiry from Tor users is if they should use a VPN to add an extra layer of protection. It encrypts data during transmission to avoid the risk of being eavesdropped.
Firewalls protect the content present in the Deep Web. The deep web is hidden from plain view, but most internet dwells in this layer. The second layer of the internet, also known as the Deep Web, exists just below the Surface Web.
Using a VPN over Tor Browser can help protect your anonymity further, among other benefits. It’s easy to let your guard down on Tor, with all the promise of anonymity. In 2015, the FBI hacked over 8,000 dark web users in 120 countries based on one warrant. Tor started as US naval research, and some still think Tor is one huge ,honeypot used to catch busy criminal bees. Not only that, Tor has over a million daily users, and only 6,000-10,000 relays at any given time. There’s a lot of content that simply isn’t available on the regular web.



