The deep and dark webs seem like illegal places you should not visit. Let’s be honest, the dark web is infamous for its criminal marketplaces, where you can find almost anything illegal for sale. A small part of the deep web is unindexed and requires a specialized browser to access. You’ll find the more dangerous content and activity at the dark end of the deep web. For this reason, users should be cautious when using their browsers.
- Tor Browser hides your location and activity, and it helps you access the dark web, but how does it work?
- The internet can be thought of as a vast iceberg, with the surface web representing the visible tip—sites indexed by search engines like Google, Bing, and Yahoo.
- But if you’re serious about maximum privacy, it’s absolutely worth the effort.
- GNUnet isn’t just a browser—it’s more of a platform for building decentralized networks.
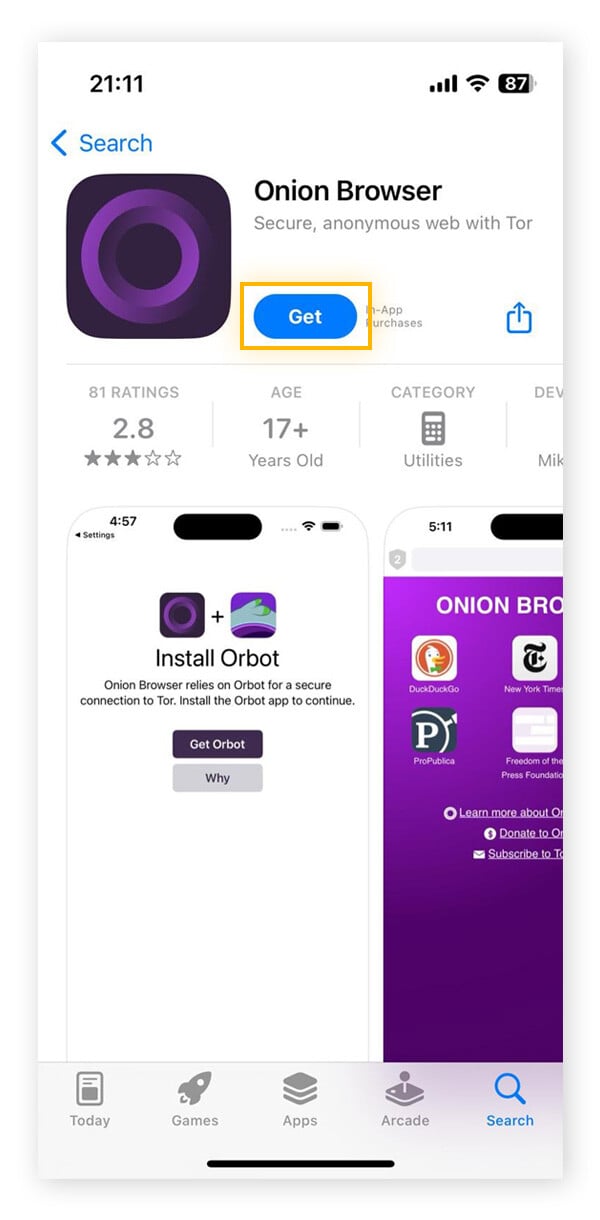
- These endorsed apps have been reviewed by the Tor Project and are considered trustworthy options for routing iOS traffic through the Tor network.
Tor, short for “The Onion Routing project,” is a free, open-source network built to protect online privacy and enable access to the dark web. If you’re new to Tor, setting up the browser software and connecting to the network might seem intimidating, but it’s actually straightforward. You’ll need a specialized dark web browser like Tor, which lets you access hidden parts of the internet while protecting your identity. Tor is a powerful tool for enhancing your online anonymity, but it’s not a complete privacy solution. Install Norton VPN to help you access content and safeguard the data you share.
Besides, victims of crime may want to hide their identities from their perpetrators. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Due to its anonymity, the dark web has attracted people who could endanger their lives by revealing their identities on the surface web.
If You Are Thinking Of Accessing The Deep Web, Remember To Use One Of These Deep Web Browsers
This masking is achieved through a sophisticated process known as onion routing, where web traffic is encrypted in multiple layers and channeled through a global, volunteer-operated network of relays. This network, often referred to as the “Onion Router,” provides a unique pathway for internet traffic, effectively masking the user’s identity and geographical location. Specialists analyze seized devices and networks to trace illegal activities back to individuals or groups. High-profile cases like the Silk Road, an infamous online black market, highlighted the extent of illegal activities facilitated by the dark web. Similarly, in the European Union, privacy laws regulate the handling of personal data and address illegal activities. Browsing legal content or engaging in lawful activities is permissible, but engaging in illegal activities is not.
- Though Apple offers strong security, Apple restricts Tor from using its normal code on macOS and iOS.
- While compatible with ".onion" services, Ahmia also filters search results to exclude potentially harmful or malicious websites.
- Start your free trial now and get true browsing privacy today.
- There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks.
- Legal frameworks focus on the content and transactions conducted on the dark web rather than the act of accessing it.
However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Many people see hacked information and stolen card data being sold on the dark web. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. An easy way to find content on the dark web is to receive a link from someone who already knows about it.
I2P: The Invisible Internet Project
The deep web is all the information that search engines cannot index or don’t have the ability (permission to index). Always double-check and cross verify before you visit an onion link. On the surface web, if you want to find something, you can simply use a search engine to look for it.

With Tor Browser, you’re assigned a unique browsing IP each time you open it. Tor’s data encryption attracts anyone who wants to keep their activity hidden, regardless of their motives. Tor hides users from anyone who might be watching, whether it’s an Internet service provider (ISP), the government, advertisers, or cybercriminals.
How Tor Browser Works
The Tor community keeps Tor running, but no top-down authority has access or control of the data. With Tor, you don’t have to worry about comments coming back to haunt you, or your internet history being tracked. Since Tor is free, open-source, and decentralized, it’s accessible to all and generally resistant to corruption. Many well-known companies such as Facebook and Twitter have .onion counterparts, and Wikipedia even has an entire list of onion services. This has led to malicious relays, where bad actors register as nodes to steal user data.

Should You Use A VPN And Tor?
On that note, if you’re having trouble telling the two apart (including their strengths and weaknesses), check out our comparison of Tor and VPNs. While Tor does a solid job anonymizing your traffic, there are still gaps, and that’s exactly where a VPN steps in. Not just to stay anonymous online, but to stop your ISP, government, or even opportunistic creepers from tracking your every move.
Tor-over-VPN Vs VPN-over-Tor: The Right Order
By requiring a second form of verification, such as a unique code sent to your mobile device, it becomes significantly harder for attackers to gain unauthorized access. Additionally, use a different password for each online account to minimize the impact of a potential breach. The Dark Web is a haven for cybercriminals and hackers, and they are constantly looking for ways to exploit unsuspecting users. Remember, encrypting your communications is an essential step in protecting your privacy and maintaining anonymity on the Dark Web. This includes using encrypted messaging apps or platforms that prioritize privacy and security. Additionally, it is important to use secure communication channels when interacting on the Dark Web.
Marketplaces For Everything Illegal
Some hospitals even have classified medical records you can’t access just like that. The same goes for private networks belonging to companies and other entities. They have their Gmail inboxes accessible only to them. Funnily enough, the deep web is the largest part of the internet. However, this part is unindexed by search engines.
Verify onion URLs
Keep in mind that you’ve to use very specific keywords when searching. Other options include Ahmia and NotEvil, which focus on listing .onion links. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results.

It uses the onion router to bounce your signal around other Tor users around the world, thereby pseudo-anonymizing you when you access the dark web. There are many legitimate websites on the dark web that can be worth visiting, but there are also the absolute extremes of illegal material, such as pornography, illegal substances, and gore. While accessing the dark web isn't necessarily wrong or illegal, it's important to know how to navigate this part of the internet safely. When you must visit the dark web, you should exercise extreme caution and avoid accessing illegal marketplaces or engaging with disturbing or extreme content. The dark web marketplaces thrive on the demand for illegal services and extreme content.
To surf the web privately, you need to connect to the Tor network from your browser. Once complete, you can add Tor to your shortcuts menu for easy access. Since its public release, researchers have discovered various vulnerabilities in Tor, which have been quickly patched. It derives its name from the encryption system, which is structured like the layers of an onion. The exit node knows where you’re going, but not who you are.
It anonymizes your traffic by routing it through multiple volunteer-run servers around the world (known as onion routing), encrypting it at each step of the way. It also adds a crucial layer of encryption before your traffic even enters the Tor network. It is worth noting that the dark web is not always illegal, as many activities take place on the dark web that are within the law.
How To Safely Use The Dark Web On Any Device
The Surface Internet is the part of the internet that we all use daily. It is time for you to open your dark web browser, Tor, connect, and start browsing. By default, Tor has ‘Standard’ level set for the security; you’d want to set it to ‘Safest.’ There you will see the security level in the ‘Security’ section. Of course, using Tor will be considerably slower than browsing with a standard web browser.
Never sign in to any account linked to your real identity (email, social media, banking, etc.) while browsing the dark web. If you’re unsure about a link, do some research or ask trusted sources within dark web communities. Be cautious of random or obscure links — these could lead to dangerous or malicious websites. Unlike the clear web, where websites are often rated or reviewed, most dark web sites are unregulated.
Disadvantages Of Using Tor Browser
It’s part of the vast deep web, which is hidden from search engines and encompasses a staggering 90% of all web content. The “dark web” refers to a part of the internet that is intentionally hidden from conventional search engines and browsers. While Google isn’t required to actively monitor illegal content, it may, however, report crimes such as child pornography. Simply browsing the dark web out of curiosity could turn into evidence of a crime, so it’s best to stay out of the dark web altogether.