Named after the web security vulnerability “Cross-Site Scripting (XSS),” the forum caters primarily to Russian-speaking cybercriminals and hackers. Selecting the top dark web hacker forums requires a systematic approach to ensure that we identify the most relevant, active, and influential platforms. Organizations must consider ethical and legal considerations when monitoring hacker forums.
Blocked Payment Gateways
Carders must choose reputable proxy services that prioritize privacy and security. To conceal their true identities and locations, carders often employ proxy services. In conclusion, credit muling may appear to be a lucrative side hustle, but the risks and potential consequences far outweigh any short-term financial gain. Credit muling refers to the act of using someone else's identity to open credit accounts or make fraudulent purchases, all in exchange for a monetary reward.
The Cybercrime Landscape: What To Expect In 2024
Closures and seizures of carding sites in 2022 have so far accounted for almost 50% of sales in the dark web stolen credit card market. Carding shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information. Card data is a hot commodity on the dark web, with credit card details and cloned cards being sold to cybercriminals. Card Shops typically host the trade of credit cards and other stolen financial information, making it easy for cybercriminals to find what they're looking for. Leaked credit cards from Telegram channels account for the overwhelming majority of compromised payment card details. Researchers gathered data from 13 dark web marketplaces, where they found over 200 listings for stolen PayPal accounts and about 400 listings for credit cards.
What Stolen Cards Are Used For
Crucially, she also outlines what service providers—including telcos, financial services, and insurers—can do to help protect consumers from carding in today’s shifting cyber threat landscape. If you fall victim to a carding scheme, you might see a negative impact on your credit score based on changes to your credit utilization ratio and potential missed payments on fraudulent purchases. But despite all this, “card-not-present” fraud, where cybercriminals use stolen card information for unauthorized online purchases, accounted for 73% of all card payment fraud in 2024, resulting in more than $10 billion in losses. And, once obtained via malware, phishing, or card-skimming attacks, the data may be sold or shared with other crooks on so-called carding forums. Once carders obtain credit card information, they test the credentials to ensure the cards haven’t been reported lost, stolen, or deactivated. After purchase, carders use automated validation and testing tools—botnets and scripts that simulate small transactions or “checkers”—to weed out dead cards and identify those safe for larger fraud.
In addition to its main website, Dark Web Informer maintains a presence on several platforms, including GitHub, LinkedIn, and Medium, where it shares cyber threat intelligence information, tools, and articles. The site covers topics such as data breaches, darknet markets, ransomware incidents, and threat alerts. While B1ack’s Stash has been most active on XSS since April 2024, it has also heavily advertised itself on Exploit, Verified, Club2CRD, WWH Club, ASCarding, and likely other forums. This incident underscores the persistent threat posed by dark web marketplaces like B1ack’s Stash, highlighting the critical need for enhanced cybersecurity measures to protect both individuals and organizations from such illicit activities. Joker’s Stash was one of the largest and most infamous dark web carding marketplaces, operating from around 2014 until it voluntarily shut down in early 2021.
PoC Released For W3 Total Cache Vulnerability That Exposes 1+ Million Websites To RCE Attacks
In 2020, customers apparently complained about the “decline in quality” of the site’s stolen data, with concerns raised regarding the validity of the posted information. Yet, while carding trends soared over the past year, the Joker’s criminal enterprise suffered fiscal setbacks. Joker’s Stash was one of the most lucrative of such carding stores (it’s estimated to have generated over a billion dollars in bitcoin during its term). Today we are one of the largest cards/dumps marketplaces.”
Partner With A Fraud Prevention Provider
Carding is the organized theft, trafficking, validation, and misuse of payment-card data that flourishes on anonymized marketplaces and forums; the dark web supplies the infrastructure for selling stolen cards, validation services, and tooling that converts data into spendable value . Site carding happens when fraudsters target a specific website to test stolen credit card numbers. In line with b1ack’s freebie marketing strategy, they announced the release of 1 million stolen payment cards for free on several popular carding forums on the last day of April this year.
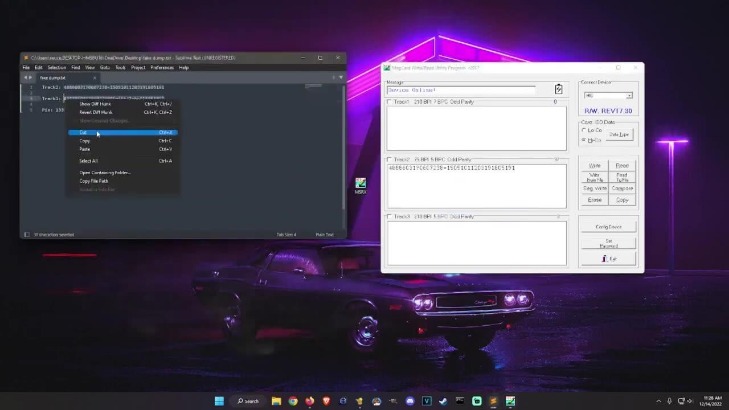
Inside A Carding Forum
- Cyberint, the Impactful Intelligence company, reduces risk by helping organizations detect and mitigate external cyber threats before they have an adverse impact.
- Integrated blockchain data for every workflow.
- Criminals frequently target websites with gift card balance check pages that have weak security protections.
- B1ack’s Stash is a relatively new but rapidly growing player in the dark web carding ecosystem.
- The merchant is liable for contactless transactions above the CVM limit that have no cardholder verification.
The key is catching this activity before large volumes of card data make it to market. Security teams monitor for telltale signs of card data exfiltration. Pattern recognition through machine learning has revolutionized how we spot compromised cards. When fraudulent transactions occur, merchants frequently end up eating the costs through chargebacks. Some focus purely on raw card data, while others specialize in “fullz” packages that include accompanying identity information. They sort cards by issuing bank, geography, and type, since platinum and high-limit cards command premium prices.
Some forums even provide escrow services to ensure secure transactions, where a trusted third party temporarily holds funds until both parties are satisfied with the transaction. Trust is a scarce and valuable resource in the underground world of carding forums. Understanding the basics of carding is essential for those seeking to navigate the underground world of carding forums. The victims of carding may suffer significant financial losses, damage to their credit scores, and emotional distress. These programs can quickly test multiple stolen card details on various websites simultaneously, maximizing the chances of successful transactions.
When NFC-based identity systems can be spoofed, the consequences could be severe across sectors relying on contactless authentication, such as physical or digital access control, payments, and transit systems. The app utilizes Host Card Emulation (HCE) to mimic a physical ISO NFC smart card by registering a service that extends HostApduService. The Malicious payloads are stored in native .so libraries (e.g., libjiagu_64.so) located in the app's private data directory (/data/data//.jiagu/).
Dark Web credit card fraud is an ongoing problem and is not showing any signs of going away. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. It offers counterfeit documents, financial fraud tools, hacking and malware services.
Cyble TIP Threat Intel

Some sites attempt to limit the number of times an individual user can repeat an action on a webpage, such as checking a gift card balance within a certain time frame. Many sites attempt to block bot attacks simply by adopting CAPTCHA methods, but CAPTCHAs often frustrate real users and drive abandonment. Security researchers are discovering more sophisticated bots that are capable of closely mirroring human behavior, making them very difficult for traditional security technologies to detect. According to KBV Research, the global digital gift card market is expected to reach $724.3 billion by 2028. Bots can attempt thousands of transactions in a short period of time to identify valid combinations at scale.
This huge growth in e-commerce has made online fraud increasingly attractive to organized criminal groups and carders. The stolen gift cards are then resold on the dark web or used to purchase goods, which are then resold for cash. When online merchants are hit with a carding attack, they often pay a heavy price as well.
Dark web forums are constantly evolving to evade law enforcement. Transactions on dark web forums typically use cryptocurrencies like Bitcoin and Monero. Many forums serve as recruitment grounds for cybercriminal groups. This data fuels various cybercriminal activities like identity theft and fraud. This ensures that messages, transactions, and data exchanges remain confidential and protected from interception. Most forum users operate under pseudonyms, further protecting their real identities.
Use Ad Fraud Prevention Tools
Sky-Fraud also facilitated discussions on carding techniques and money laundering tips. This process is known as “carding”, and it has become a key part of the cybercriminal’s playbook. The data includes the service code, PIN code, and card verification code, making it highly valuable for thieves. Credit card details can be sold as digital items on the dark web, with the basics costing around $17.36. The resulting financial loss from stolen information is tremendous, not only for the individual victim but also for the financial provider and any involved organizations. Group-IB’s cybercrime research unit has detected two major leaks of cards relating to Indian banks in the past several months.
However, not all proxy services are created equal. By using proxies, carders can mask their true IP addresses, making it difficult for law enforcement agencies to trace their activities. These services act as intermediaries between the user and the target website, routing internet traffic through different IP addresses and servers. It is crucial for carders to stay updated with the latest software versions and exercise caution when using them.
- The cost of mitigating carding incidents, updating systems and addressing security gaps can be substantial.
- Experts suggest that this giveaway serves as a marketing ploy to attract new users to B1ack’s Stash and establish its dominance in the competitive carding market.
- This means you would be able to see the most relevant threats to your organization, have the messages translated from its original source language to English, contextualize threat actor jargon, and provide a risk score among many other analysis tools.
- The shutdowns have led to discussions about operational security, as some forum members fear they could also be arrested.
- It was known for selling high-quality stolen payment card details and used blockchain-based domains to evade law enforcement.
- These services help criminals execute complex schemes and evade detection.
It has gained a reputation for its professional approach and the high quality of its content, attracting a sophisticated and experienced user base. "The wave of recent departures has potentially been a trigger for UniCC's retirement, as illicit actors see an opportunity in the turbulence to either run away with users' funds or retire to avoid increased law enforcement attention," the researchers said. The UniCC team also gave its users 10 days to spend their balances, while also warning customers to "not follow any fakes tied to our comeback." EMV stands for “Europay, Mastercard, and Visa,” the companies that initiated the chip standard. “As currently there are no widely used technologies that can completely clone bank card EMV chips, we expect cybercriminals specializing in harvesting bank card dumps to encounter further challenges,” Group-IB said in a statement. New marketplaces include All World Cards, BINART, CC Shop, Dundee Shop, Flowcc, Hogwarts Market, Rockefeller’s Store and Wixxx, according to threat intelligence firm Intel471, but “no dump shop or threat actor has been able to fill the void” left by Joker’s Stash.