Telecom service vendors are now purchasing the existing dark fiber & also aim to develop their own,...
Registration was mandatory to access the Silk Road (like most darknet platforms). The users on this site...
The dark web, a subset of the deep web, operates on encrypted networks like Tor, requiring specialized...
Due to the decentralized nature of these markets, phishing and scam sites are often maliciously or accidentally...
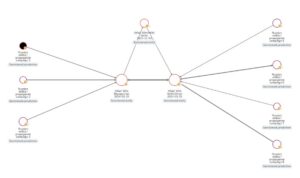
You can pass a file containing Cypher statements as an argument when running cypher-shell. The TAR distribution...
In this article, we’ll dive deep into the hidden world of the Dark Web, exploring its origins,...
Visiting the dark web, though, is different than accessing the deep web. Hackers and others, then, won’t be...
Adopting these practices ensures theme systems remain scalable and maintainable as applications evolve. These validation techniques help...
It is common to hear news reports about large data breaches, but what happens once your personal...
Historically when darknet sites close down, the operators disappear with customers' or vendors' money – this is...