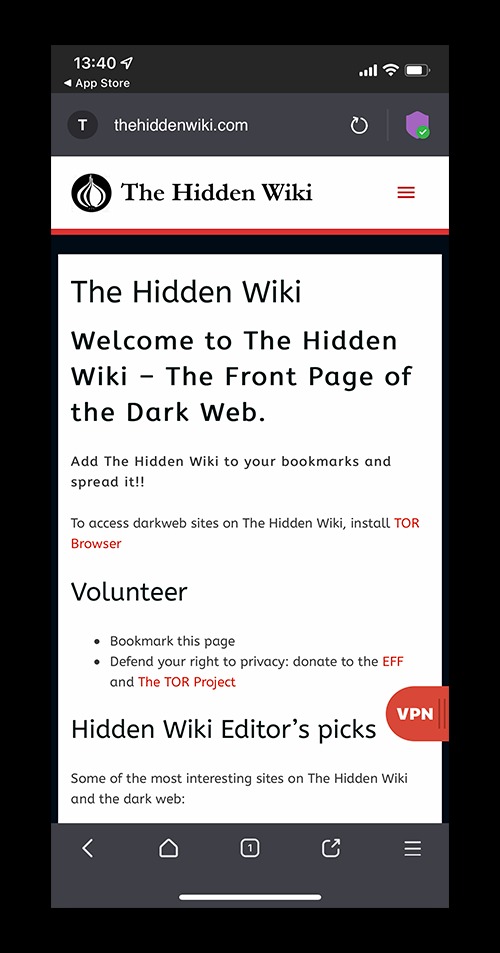
The best secure dark web browsing tools include the Tor Browser, Tails OS, and VPN services. Yes, several dark web forums list communities focused on privacy, security, and research. These sites often feature verified and regularly refreshed top Hidden Wiki links. It’s best to explore other secure dark web browsing tools and sites like Hidden Wiki. While it lists many top Hidden Wiki links, the platform can also include unsafe or outdated sites.
What Is A Class Action Lawsuit?
- Ransomware gangs are also expected to diversify their tactics, targeting smaller companies and individual users to maximize their reach.
- Look for hidden wiki updated links on reliable alternative dark web directories like Ahmia or DeepSearch.
- The dark web is a small, intentionally hidden subset of the deep web that is specifically built for anonymous communication.
- Ahmia filters its results to block illicit content and harmful sites.
- Bohemia accepts Monero and Bitcoin as payment methods and places a strong emphasis on protecting user anonymity through PGP encryption.
- The deep web refers to any part of the internet that is not indexed by search engines.
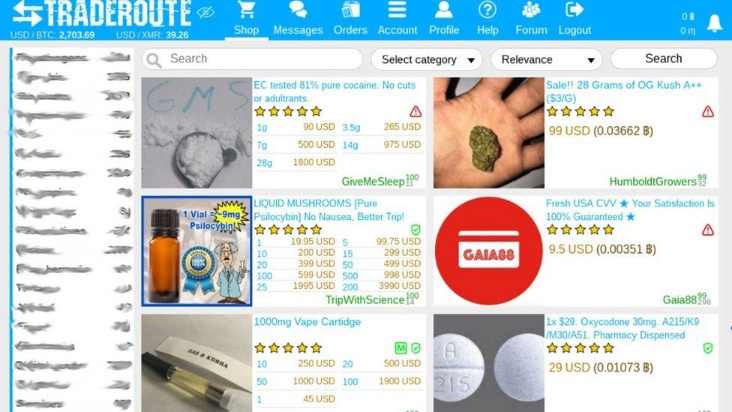
Features such as escrow, PGP encryption, and the use of multi-signature wallets are good indicators of a trustworthy marketplace. Look for markets with strong reputations, verified vendors, and positive user feedback. Additionally, use privacy-focused cryptocurrencies like Monero, which offer stronger anonymity features than Bitcoin. Yes, most of these marketplaces allow vendors to list their products or services.
Whether it's evaluating the effectiveness of marketing software or the security features of digital wallets, our reviews are a reliable resource for those in the know. Our meticulous reviews, based on hands – on experience, are designed to assist businesses in selecting the right tools for growth. By closely monitoring market movements, we offer in – depth analysis that empowers businesses and individuals to make strategic decisions. Go-Beyond.biz is a trailblazing force in the digital business realm, specializing in online shopping, content creation and marketing, digital finance, and cryptocurrency.
What Are Onion Sites?
In fact, there are growing concerns about law enforcement monitoring what is happening on the dark web. Government authorities across the globe are taking over many Tor-based sites. Some services are genuine; you can get what you want at an agreed fee. Many services that are allegedly offered on the dark web are scams.
Use Verified Links To Ensure You Stay Safe On The Dark Web
The dark web is often considered to be a dangerous sector of the web, is where criminals buy and sell drugs. You’ve probably heard the term “dark web” and wondered what it’s all about. This is why we recommend bookmarking this page so that you may always have quick and secure access to the top dark web destinations available. We check all v3 Onion links before we add them, and remove fraudulent items on a regular basis.

Benefits Of Using Forest VPN With Tor
Explore the leading dark web marketplaces, offering secure, anonymous platforms for digital goods and services. For specific questions about your eligibility or claim, contact the settlement administrator or consult with a qualified attorney. You don’t need to hire your own attorney to participate in the settlement.

Unlike conventional web crawlers, they have to contend with slower load times, inconsistent site availability, and often sparse interlinking between sites. The result is an entirely separate ecosystem of data that's invisible to the clear web. This process is ineffective on the dark and deep web, where most sites are not interlinked. For businesses and cybersecurity professionals, however, they are a critical instrument. For the casual user, navigating this space is fraught with risk. Yet some of today’s biggest risks—such as data breaches, identity theft, and corporate espionage—often originate on the dark web.
Drug Trafficking Sites
- This is an outstanding feature when accessing dark web markets, forums, or even deep web archives.
- Privacy-focused internet users who access onion sites may see greater anonymity while browsing or sharing sensitive information.
- Our meticulous reviews, based on hands – on experience, are designed to assist businesses in selecting the right tools for growth.
- Deep-net.link is not liable for any loss or damage incurred as a result of using the above links.
As AI becomes more accessible, hackers may use AI-driven tools to automate data theft on a massive scale. Infostealer threat actors specialize in malware that harvests personal data without consent, such as login credentials, bank accounts, and social security numbers. These groups operate globally, leveraging sophisticated tools and networks to execute large-scale attacks and maintain anonymity.
Businesses should prepare for more sophisticated ransomware campaigns, potentially leveraging AI to exploit security gaps. These groups often operate on a ransomware-as-a-service (RaaS) model, renting their tools to affiliates in exchange for a share of the profits. Crypto-laundering threat actors specialize in stealing and hiding the origins of their cryptocurrency. The proliferation of IoT and 5G devices will provide new attack vectors for infostealer gangs. Their tools often spread through phishing campaigns or compromised software downloads, enabling crimes such as identity theft.
AI-Powered Threats
The deep web has much more to offer than just markets — it is a collection of knowledge, communities, and tools. This is an outstanding feature when accessing dark web markets, forums, or even deep web archives. While some anonymity is present with the Tor browser, a VPN adds a second layer of protection and anonymity to your browsing experience.
These sites aren’t accessible via standard web browsers or search engines. The dark web is just a part of the internet where users can communicate and browse privately, often beyond the reach of standard government monitoring. Search engines and corporate websites might be OK, but even a popular Tor website like Hidden Wiki can show illegal deep web links that jeopardize your online safety.
After the shutdown of RaidForums, BreachForums filled the gap by hosting discussions on exploits, data leaks, and cybercrime. Launched in March 2022 as a successor to RaidForums, BreachForums quickly became one of the leading forums for discussing data breaches and sharing stolen information. It is heavily business-oriented, with sections dedicated to ransomware services and cyberattacks. Initially known as DaMaGeLaB, the forum rebranded in 2018 after the arrest of one of its administrators.
These sites are often closely monitored by law enforcement agencies and are illegal to access or participate in. These sites offer access to illegal streaming of pirated movies, TV shows, sports events, or other copyrighted content, often in high quality. These platforms provide services related to illegal activities, such as hacking tools, malware, ransomware, or services for hire (e.g., DDoS attacks, identity theft). The deep web consists of unindexed content not accessible via standard search engines. This is the publicly accessible portion of the internet that can be indexed by search engines.
An easy way to find content on the dark web is to receive a link from someone who already knows about it. It relies on P2P connections and requires specialized tools and software. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. As a result, you cannot find them with a regular search engine. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
These search engines crawl the deepweb links & URLs and return results just like a surface-level search engine would—but anonymously. If you’re looking to search links on the deepweb, Ahmia and NotEvil are great tools. Smartmixer made it harder to trace funds on the blockchain, although malicious actors could misuse such tools for illegal transfers. Over time, the technology became public, and people began using it to create private networks and hidden sites.



