Proton Mail’s dark web version provides end-to-end encrypted email with enhanced privacy protection. I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. My testing showed it loads quickly and offers the same high-quality content as its regular website, making it an excellent resource for readers in censored regions. ProPublica provides Pulitzer Prize-winning uncensored investigative journalism through its .onion service. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need.
Should You Use A VPN And Tor?
Many transactions conducted on the Dark Web involve the exchange of cryptocurrencies, as they offer a level of anonymity that traditional currencies cannot. By offering secure communication channels, it gives people in oppressive states the opportunity to connect with the outside world and engage in activism without facing the consequences of being identified. Activists in countries like China, Iran, and Russia use the anonymity provided by Tor to discuss sensitive political matters, organize protests, or disseminate information that might be suppressed by state authorities. Hackers also use the Dark Web to exchange tools, tips, and techniques for breaching computer systems, creating a thriving ecosystem for cybercrime. Stolen databases from large corporations and government agencies are frequently sold to the highest bidder.
Cyble TIP Threat Intel
- So while the tool itself isn’t illegal, using it for criminal purposes can land you in serious legal trouble.
- Although it’s no longer active, it’s setting the standard for coming onion links.
- People can contact assassins on the dark web who are ready to kill for money.
- This makes it difficult for interlopers to monitor the traffic or trace any legal or criminal activity back to you.
- Indexes of website links allow Google and other search engines to return relevant results whenever a user types a keyword into the search bar.
Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent. People who live under a government that deeply supervises or censors internet traffic eventually get attracted to the dark web. As much as the Darknet contains even the “good” stuff, it’s not a place you need to stumble about blindly without proper dark web safety.
Legal Uses Of The Dark Web
If you’ve been part of a data breach, your information may be sold or leaked on the dark web. ✅ Want to monitor the dark web for threats to your organization? For online security professionals and C-suite executives, awareness is the first step to effective cyber risk management. Third-party vendors may unknowingly expose your data on the dark web. Yes, law enforcement agencies can track users anywhere on the internet.
History Of The Dark Web
Like any other area of the internet, the danger involved depends on how people choose to use it. Malicious websites, compromised Tor nodes, or accidental downloads can expose your device to malware or hackers. To stay safe while browsing on the dark web, tools like Norton 360 and a reliable VPN are essential. That’s why, if you’re planning on using the dark web for legal, privacy-focused reasons, it’s important to stay protected. Unlike the public web, it can’t be accessed through standard tools like Google, Firefox, or Chrome.
- Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble.
- We’ll also discuss why it’s dangerous and why you should inform yourself about the dark web even if you don’t plan to be on it.
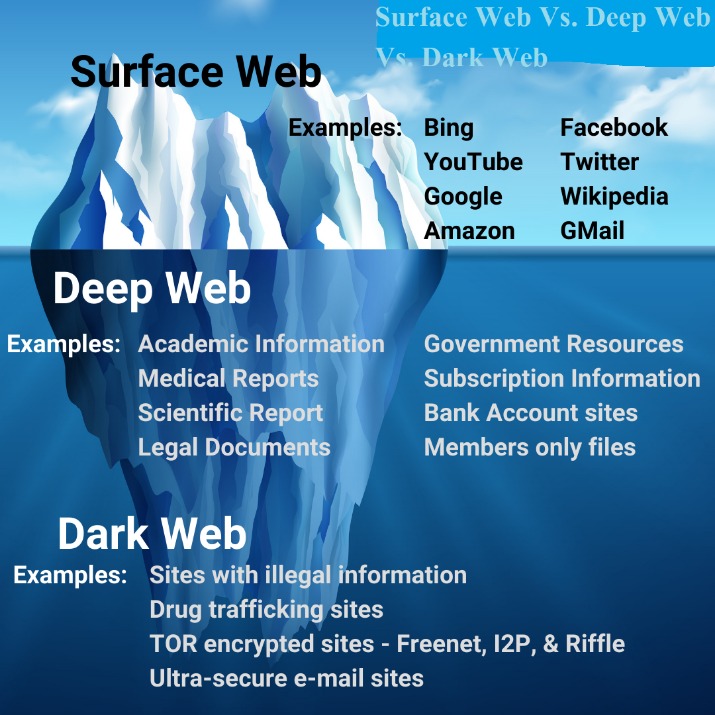
- The dark web is part of the deep web and is hosted on darknets and encrypted networks like Tor, Freenet and Riffle.
- Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves.
- In a world of bulk data collection, surveillance, and personalized ad tracking, it's up to us to take control of our personal privacy.
- These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers.
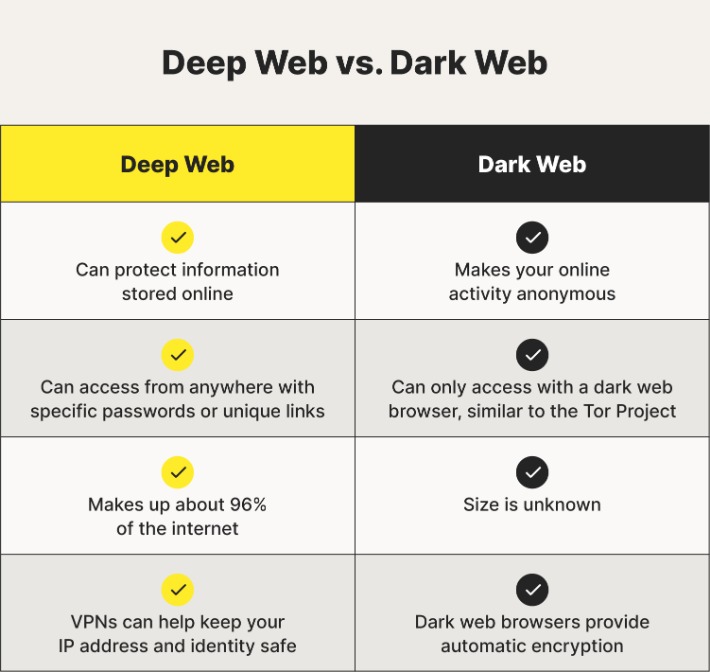
The dark web, by contrast, is configured on darknets — online networks that can be accessed only with special software and techniques. The dark internet is designed to provide anonymity by keeping communication private through encryption and routing online content through multiple web servers. Despite its reputation for privacy and security, the dark web is home to scams, phishing sites, and malware targeting unsuspecting users. Using these search engines can help you find and explore sites on the dark web more efficiently.

Can I Protect My Privacy Without Going Onto The Dark Web?
We didn’t give them any information, but it’s scary to think how legitimate they sounded in the email. They asked for our personal information in exchange for access to the forum. Phishing is when someone contacts you pretending to be someone else to gain access to your personal information, which often results in identity theft. If you think eBay transactions aren’t safe, dark web transactions are far worse.
The History Of The Dark Web
Let’s take a closer look at it to see just how dark the dark web can be. Dark0de alone had over 69,000 listings, while Torrez offered around 57,000.2 By far the most infamous dark web marketplace is the Silk Road. A range of underground marketplaces populate the dark web. You can access most of the deep web using a normal browser.
Is The Dark Web Illegal?
These search engines work best if you already know what site you’re looking for, not for general browsing. Other options include Ahmia and NotEvil, which focus on listing .onion links. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. If you want to find its current links, you can search for terms like “Daniel replacement.” Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together.
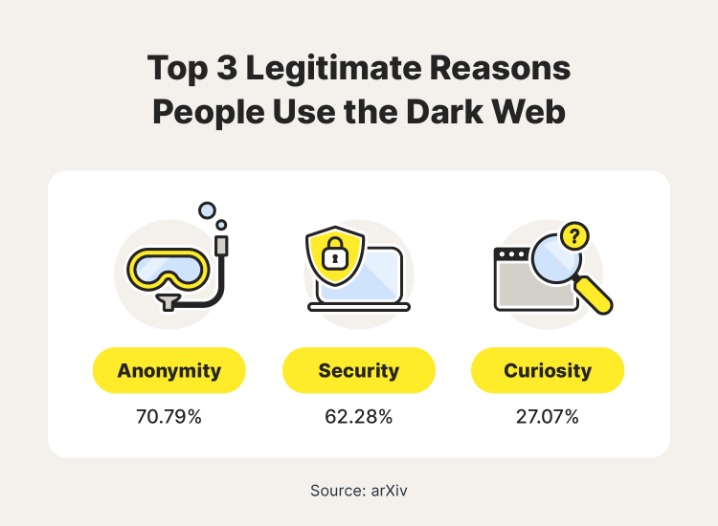
Engaging in any of these activities is a serious crime with severe consequences. This makes it nearly impossible for anyone to trace your online activity back to you. When you use the Tor browser to visit a site, your connection is wrapped in multiple layers of encryption, like the layers of an onion. Their IP addresses are obscured, so you can’t easily discover who is hosting the site or where it’s located. This anonymity serves many purposes, both good and bad. This same technology was later released to the public, allowing anyone to browse the internet without being tracked.
However, extra caution is advised—use a good VPN and ensure the security settings of your device are up to date to minimize risks. The dark web came into existence as an offshoot of government experiments with anonymous communication. Download and install Tor first, and optionally a VPN for added security.
Anyone with a browser and internet connection can access these pages without special tools or permissions. This includes news sites, blogs, online stores, and social media platforms. The dark web plays a crucial role in cybersecurity, serving both as a threat vector and a valuable intelligence source. DuckDuckGo is the best dark web search engine, as it offers an excellent user experience akin to surface web search engines. To access the dark web, you need an anonymizing web browser or any browser that supports the Tor network. No, the dark web isn’t illegal, but what you do while in the underbelly of the internet matters.
Unlike the public “surface web,” dark web sites are deliberately concealed and require specialized software to access, the most well-known being the Tor (The Onion Router) browser. Naval Research Laboratory, and the Tor Project, starting early 2000s, put this technology into the public domain, giving rise to the dark web. Despite the sinister name, the Dark Web is only one part of the overgrown internet that is much larger than what most search engines show. The dark web will continue to develop with the help of new anonymity technologies, changes in legislation, and the needs of users. The confusion comes from the fact that both are invisible to search engines, however, the usage of the dark web requires specific software such as the Tor browser. The idea that there are only malicious or technical gurus does not reflect the truth that the onion services draw all sorts of people.



