From cybersecurity and physical safety to risk management and emergency preparedness, we cover it all with a preventive mindset. He holds a BA in history from Yale and is currently pursuing graduate studies in computer science at UT Austin. The dark web remains a mysterious part of the internet, offering both benefits and potential dangers. Despite its association with illicit activities, the dark web is also used for legitimate purposes. Tor routes data through multiple volunteer-operated servers, or “nodes,” disguising the original IP address and location.
Tools Needed For Safe Access

There are various sites on the dark web dedicated to the distribution and discussion of hacking tools, cyberattack services (such as DDoS attacks), and information on data breaches and leaks. These platforms provide services related to illegal activities, such as hacking tools, malware, ransomware, or services for hire (e.g., DDoS attacks, identity theft). Some dark websites serve as platforms for whistleblowers to anonymously share sensitive information.
How To Access The Dark Web And Deep Web Securely
The surface web includes anything you can find by entering terms into a search engine like Google. With expert analysis and practical solutions across consumer electronics, software, security, and more, PCMag helps consumers make informed buying decisions and get the most from their tech. For over 40 years, PCMag has been a trusted authority on technology, delivering independent, labs-based reviews of the latest products and services. PCMag.com is a leading authority on technology, delivering lab-based, independent reviews of the latest products and services. I tend to read app privacy policies to see what kind of data companies collect, and as a result of those findings, I don't use many mobile apps. I like testing new software for work, but I'm less "plugged in" to the internet than I used to be.
- Learn more about our editorial team and our research process.
- If you exercise due caution and use a combination of the Tor browser and common sense in which sites you access on the dark web, yes, the dark web is safe to use.
- I also report on online scams and offer advice to families and individuals about staying safe on the internet.
- That means that I2P can’t visit “.com” or “.onion” sites because the network is not connected to these servers.
- Dark web browsers and search engines do a lot of work to mask user identities, but you’re never completely untraceable.
- If you really want to visit dark web forums or sites for some reason, you'll need to take some serious precautions to protect yourself and your devices.
Yes, people have been arrested for certain activities on the dark web. Agencies also trace crypto transactions, scrape data from seized servers, and sometimes deploy malware to reveal users. NSA leaks revealed that the CIA uses a system called XKeyscore, which flags users based on Tor activity, search terms, and browsing behavior — even on the surface web. Global agencies use powerful tools to monitor, infiltrate, and bait users. Think news websites, social media platforms, shopping sites, YouTube, Netflix, blogs, Wikipedia, recipe sites, and many others.
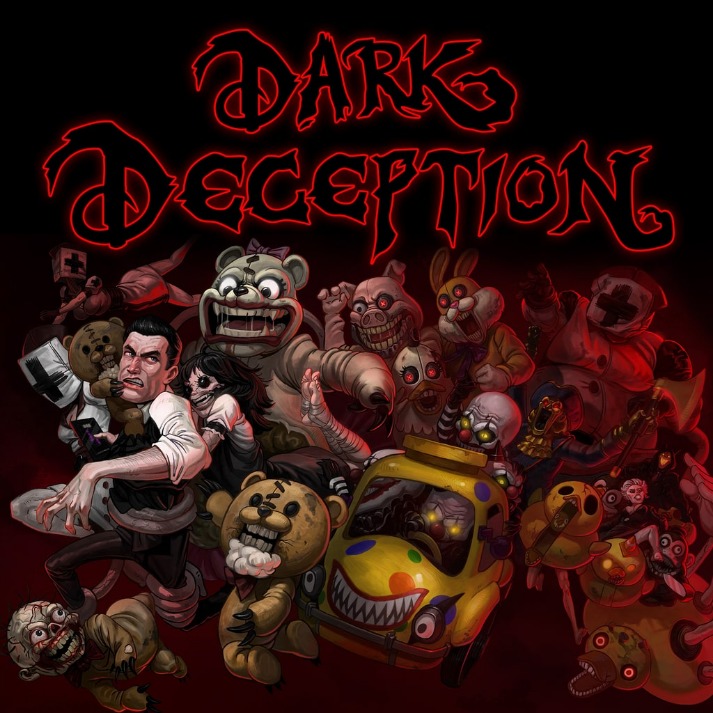
What Are Ransomware Leak Sites
The dark web, by contrast, is configured on darknets — online networks that can be accessed only with special software and techniques. The websites you visit every day aren't all there is to see on the internet — not even close. Don’t click on suspicious links, be skeptical of what you read, and avoid dark web marketplaces if you don’t want to stumble on illegal activity or content. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too.
Use trusted resources to find safe sites and stay aware of the risks involved. These addresses are designed for the Tor browser, the most common tool for accessing it. The dark web is used for a variety of purposes, both legal and illegal. In one of the most famous examples, the FBI took down Silk Road, one of the largest illegal marketplaces to ever exist. If you’re doing something illegal, there’s a real chance someone’s watching. In short, you can get some privacy, but you can’t get total anonymity.
Should I Only Use A VPN To Access The Dark Web?
To look at it in a different way, it makes up between 90% and 95% of the internet. It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities. Sites in the dark web have .onion as their domain in their URLs. You can also use Brave to access the dark web on your computer. This will protect your privacy and add another layer of security, keeping your browsing private from your ISP, cyber attackers, and other third parties.
Verify All onion Links
These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. As always, protect yourself from online threats with mobile Android security or iOS security software. Before accessing the dark web, install strong security software to help keep your device protected.

To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found. It’s possible to buy and sell illegal drugs, malware, and prohibited content in darknet marketplaces. But there are also many illegal activities that happen on the dark web. The dark web limits online tracking, and there are many legitimate reasons people like journalists and activists use the dark web to remain private.
Data Sheets
The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people). You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it. To access the dark web safely, it’s necessary to use a dark web browser like Tor in combination with trusted dark web directories and search engines to help you find reliable sites. The dark web is a hidden part of the internet where users are anonymous and can access illegal marketplaces and hacking forums and partake in illicit activities.

Cyble Partner Network (CPN) Join Us
Visiting the dark web carries significant risks, especially for users unfamiliar with its structure and threats. The anonymity of cryptocurrencies and direct user connections makes it a lucrative ecosystem, powering both small-scale attacks and large ransomware campaigns. Tools, malware, and stolen data, including credit card information and personal identities, are commonly traded. The dark web acts as a marketplace and networking hub for hackers and cybercriminals. Marketplaces offer illegal goods such as drugs, weapons, and counterfeit documents, often priced in cryptocurrencies for untraceability. While detractors argue its use for activism invites political instability, proponents see it as a vital tool for transparency and dissent against oppressive regimes.
As Spyware Companies Get Chummy With White House, Apple And WhatsApp Say They’ll Protect Your Phone
Fraudulent activities on the dark web include phishing scams, fake identity sales, and the sale of fake products. Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information. Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web.
The dark web refers to content on the internet that is intentionally hidden and requires special software like Tor Browser to access. As when visiting ordinary websites, stay alert to security risks on onion sites. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. The deep web is the part of the internet you can’t access through search engines like Google and Bing. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found.
It even prompts you to switch to a site’s .onion version if one is available. It offers standard features like image, video, and news searches, but also includes tools like anonymous chat, AI search results, and secure browsing. Ahmia consistently delivers accurate results and makes it easier to browse without accidentally stumbling onto disturbing or harmful content. You can sort results by date, which helps when you’re looking for recently updated or new sites.



